Jason Duff
- Home /
- Authors | Associates /
- Jason Duff

Jason Duff
CISSP | Seasoned Cybersecurity Practitioner and Technology Generalist. 25 Years of industry experience across a broad range of technologies, industries and Security Domains.
The Personal Liability Trap and Evolving Regulatory Volatility
The illusion of Cybersecurity maturity is causing boards and IT leaders to prioritize technology trends and rapid innov...
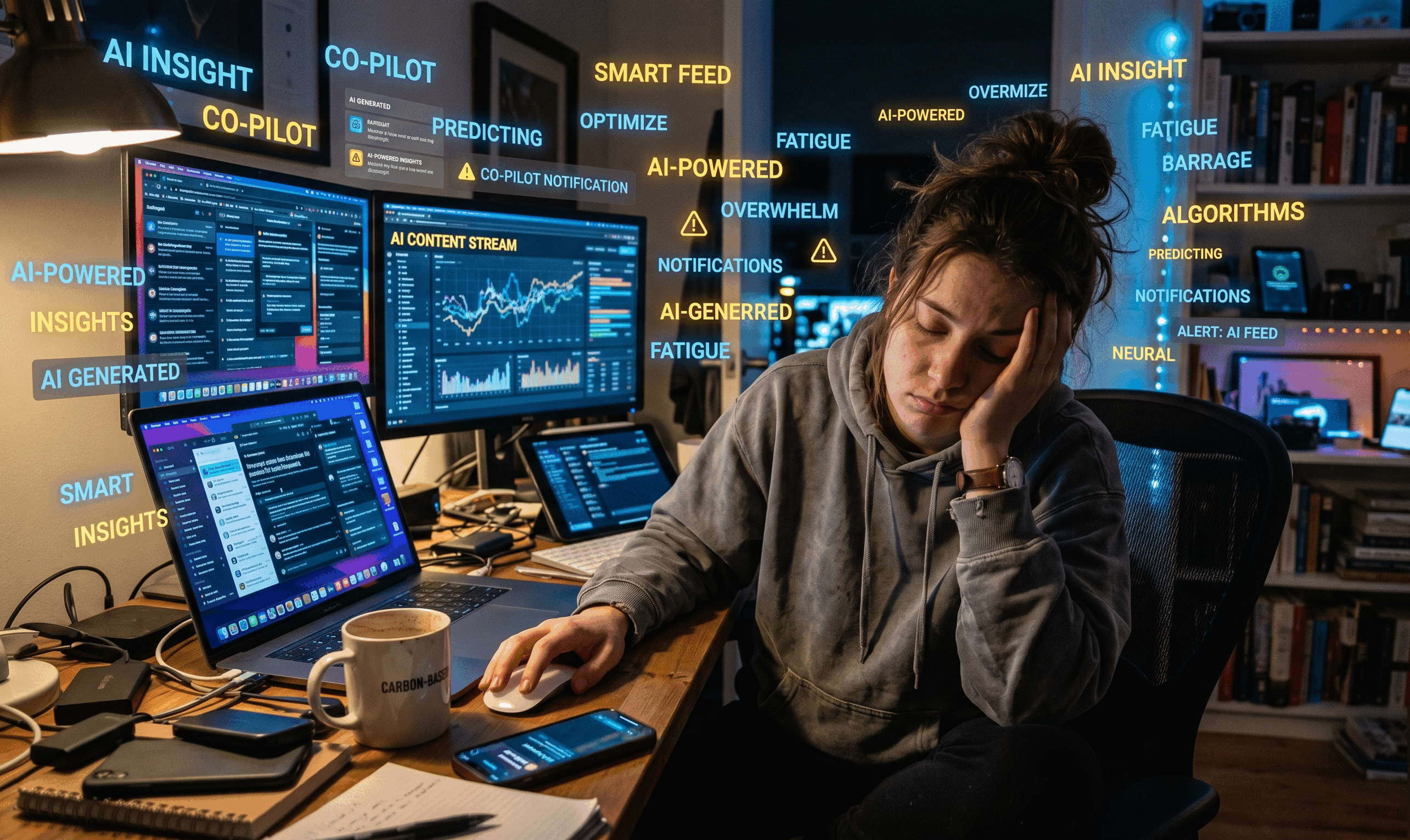
AI Fatigue is real, and we are all living it
It is difficult, if not impossible to not be subjected to AI in one way or another all day, every day. It is exhausting...

The AI Security Maturity Model
A Practical Framework for IT Leaders to Assess Readiness and Close Gaps in Agentic AI Security

A Multi-Front War in Cyber Security
The Rise of Advanced, Multi-Stage Attacks: Several reports highlight the increasing complexity of cyberattacks. We&rsquo...

The AI-Powered Ransomware Surge: Are Cybercriminals Getting Lazier or Smarter?
Recently we have seen threat actor tactics shifting towards an escalated use of artificial intelligence (AI) to enhance ...

Gmail Security Upgrade: QR Codes Replace SMS for Enhanced Authentication
Google’s announcement to replace SMS-based two-factor authentication (2FA) for Gmail with QR is a significant shif...

DeepSeek Cybersecurity Nightmare for Individuals and Enterprise
We have recently seen several significant cybersecurity stories, but one has consistently dominated headlines: the DeepS...

Elon Musk's DOGE A Cybersecurity Nightmare?
February 13th, 2025, marked a significant escalation in cybersecurity concerns surrounding Elon Musk’s Department ...
Ban of DeepSeek by Taiwan: A Cybersecurity Wake-Up Call
Today’s dominant cybersecurity story centers around the ban of DeepSeek by Taiwan, citing serious national securit...
The DeepSeek AI Data Leak and its Global Fallout
February 11th, 2025, saw the continued fallout from the DeepSeek AI data leak, a story dominating cybersecurity headline...

Zyxel's Unpatched Zero-Day Vulnerabilities: A Cybersecurity Crisis in the Making
February 8th, 2025 marks a critical point in cybersecurity with the escalating impact of unpatched zero-day vulnerabilit...

DeepSeek Malware Distributed via Fake Packages. Potential Cybersecurity Crisis
Today’s most significant cybersecurity story revolves around the malicious distribution of DeepSeek malware disgui...

Deepfakes and the $25 Million Heist: A New Era of Cybercrime
The cybersecurity world is buzzing about a disturbingly sophisticated attack that highlights the evolving nature of atta...

The Fall of Major Cybercrime Marketplaces
Today’s most significant cybersecurity news isn’t about a single vulnerability or a specific company breach;...
The Rise of AI-Powered Attacks and the Urgent Need for Enhanced Defenses
The cybersecurity landscape is dominated by a confluence of escalating threats and evolving defensive strategies. The ov...

LinkedIn's AI Training Lawsuit: A January 2025 Cybersecurity Flashpoint
As of January 30th, 2025, a significant cybersecurity story dominating headlines is the lawsuit against LinkedIn for all...

Disable Local Administrator Accounts to Thwart North Korean Cyber attacks
The most significant cybersecurity story on January 29th, 2025, centers around an urgent warning issued by the FBI regar...
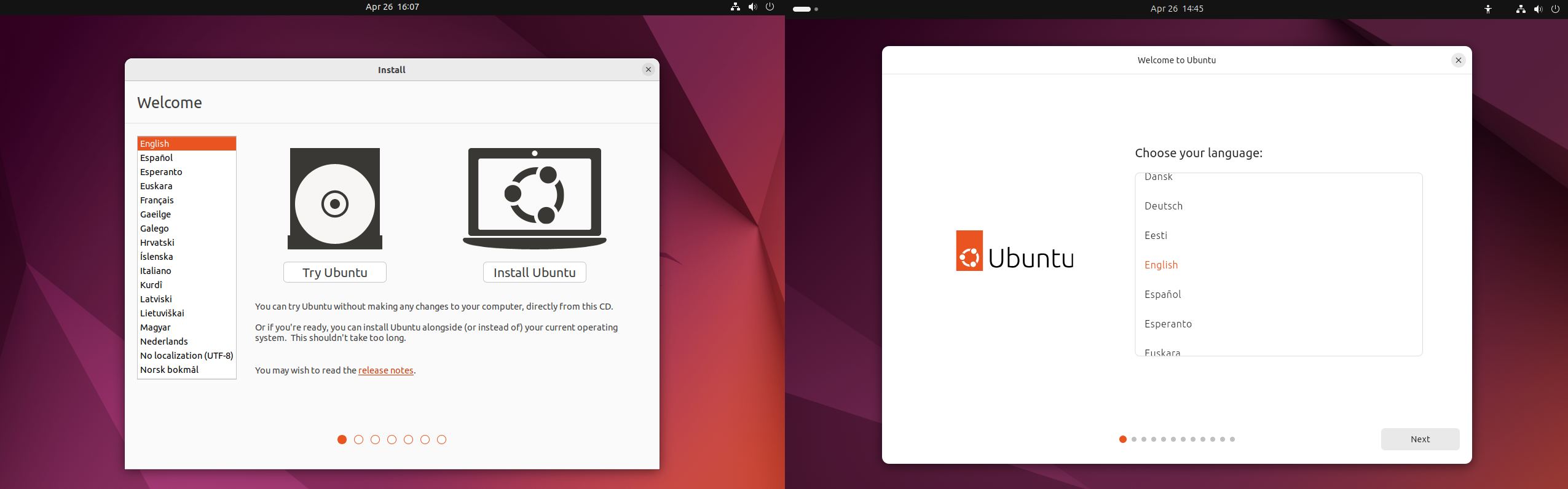
Ubuntu 24.04 | New features, new look, new technology, but is it worth the upgrade?
The all new Ubuntu 24.04 is here! Ubuntu has released their latest LTS version, Ubuntu 24.04 Noble Numbat, so I decided ...
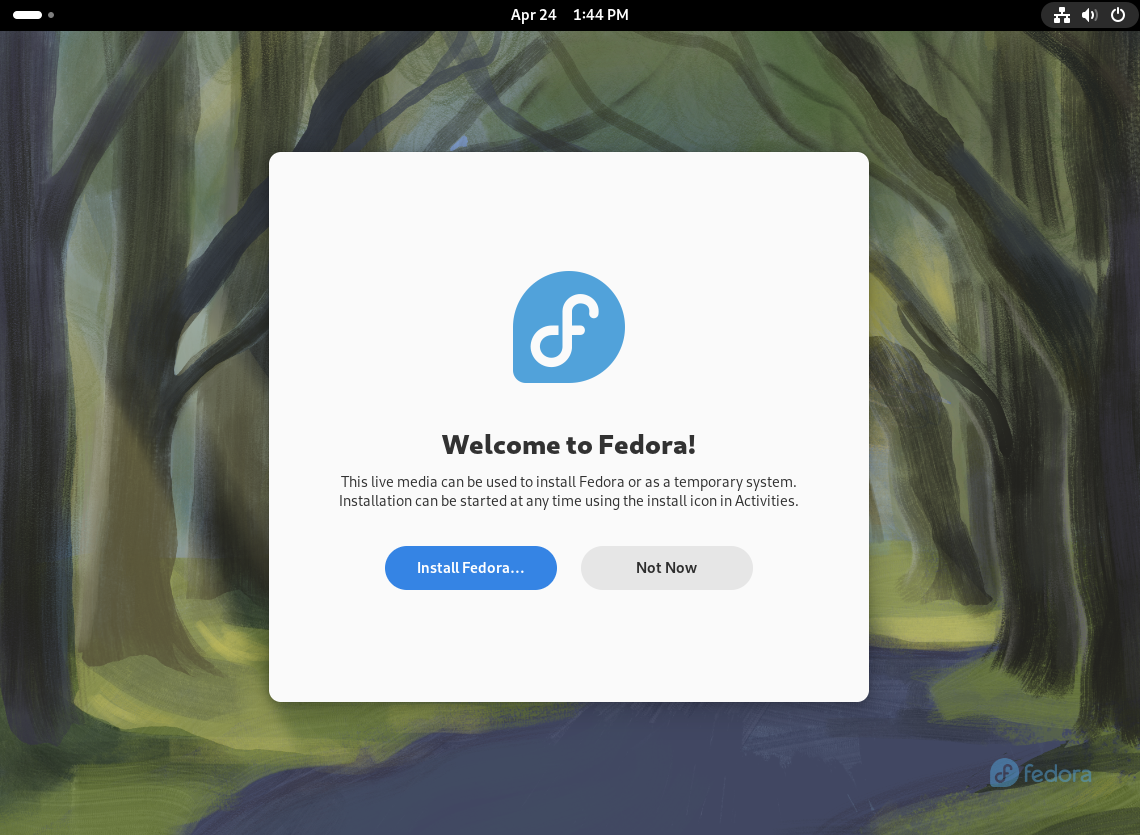
Fedora 40 | First Impressions from a Debian user
If you have read any of my other ramblings, you may have picked up on the fact that I am almost exclusively a Debian (va...
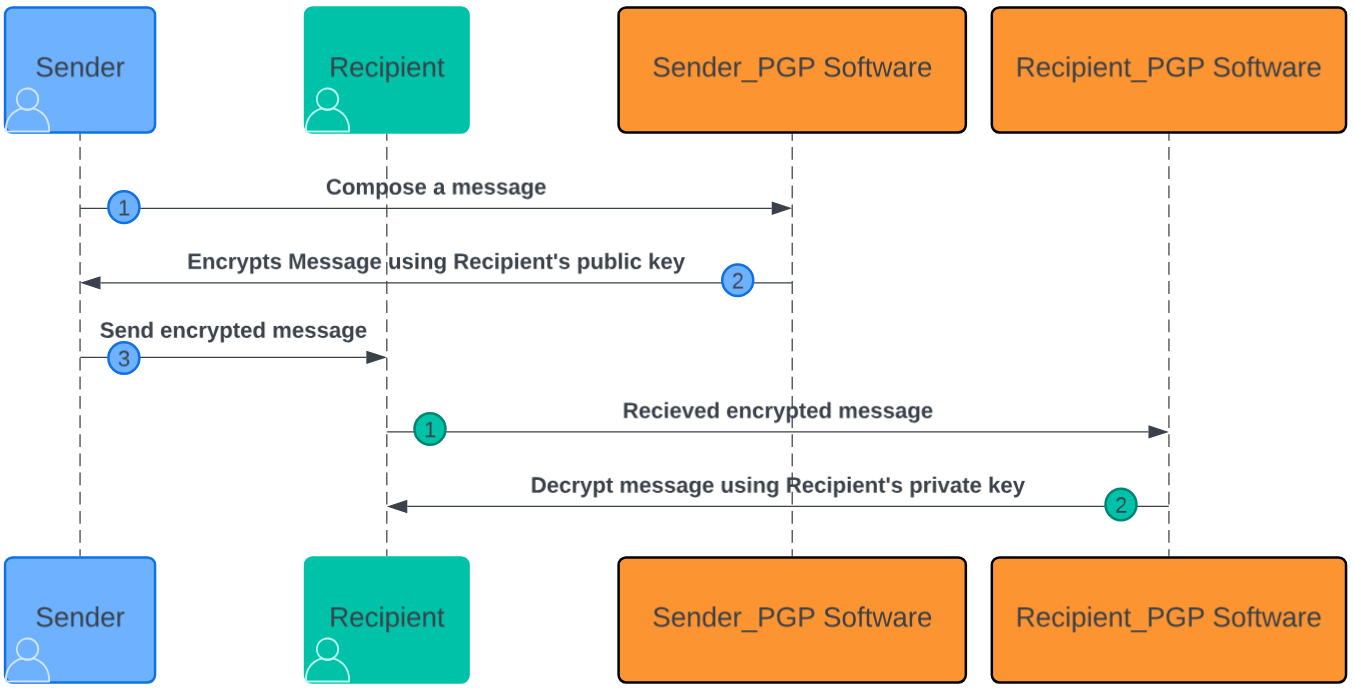
PGP | What is it and how to use it?
PGP stands for ‘Pretty Good Privacy’ but it is much more than that. It is the open source gold standard mech...
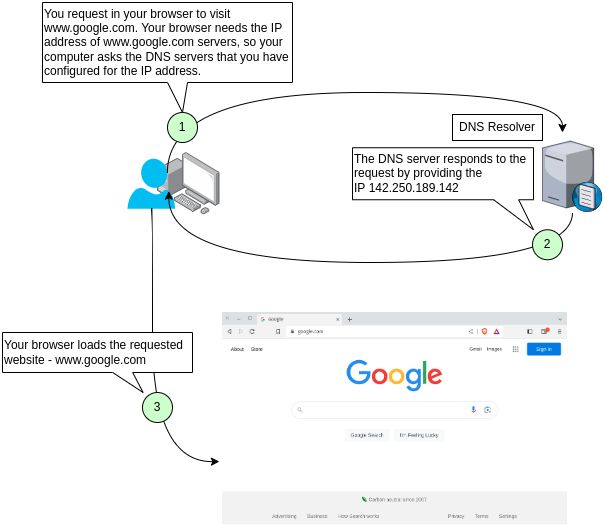
DNS Tutorial | How the Domain Name System works.
Today I thought I would give a basic overview of how the Domain Name System (DNS) works and explain a bit about the most...
Linux | Is it right for me and how to Install it
Over the years, I have spoken to countless individuals who are not necessarily ’tech savvy’ about Linux and ...
My favorite Linux Distributions and Why
Updated 2023/02 Today I thought I would take a break from all of the technical articles and write something a little mor...
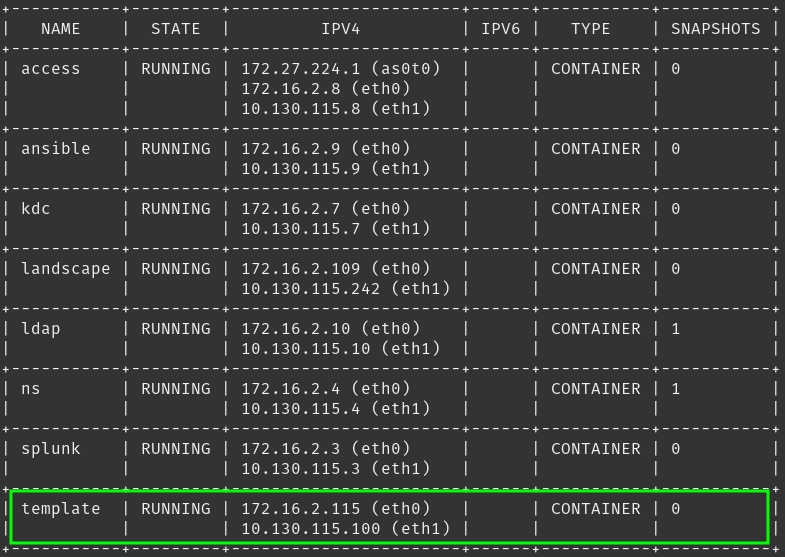
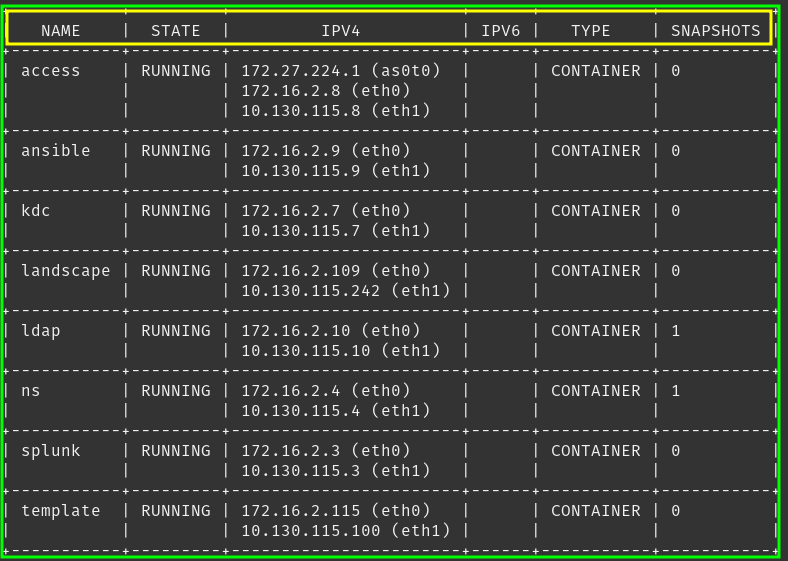
Ubuntu 22.04 | Configure LDAP/Kerberos Client Authentication
Adventures in the LXD Lab | Authentication Services Now that I have a fancy new authentication system (Kerberos and LDAP...
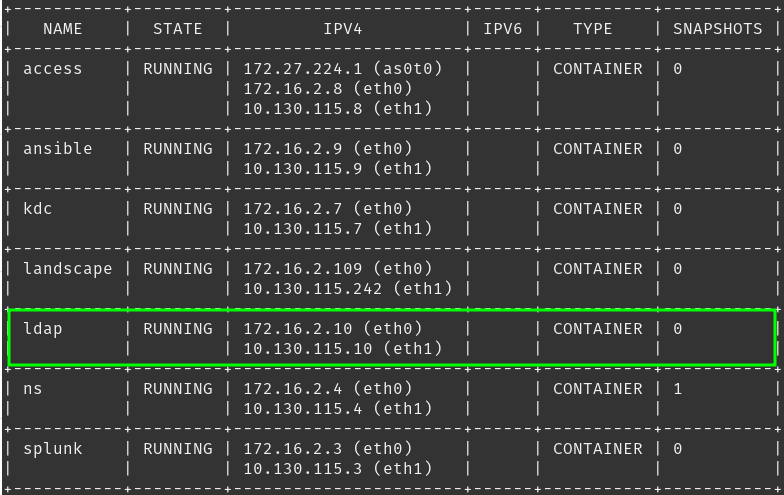
Ubuntu 22.04 | Install and configure an OpenLDAP Server
Adventures in the LXD Lab | Authentication Services Tinkering is what I do but this article goes a bit beyond tinkering ...
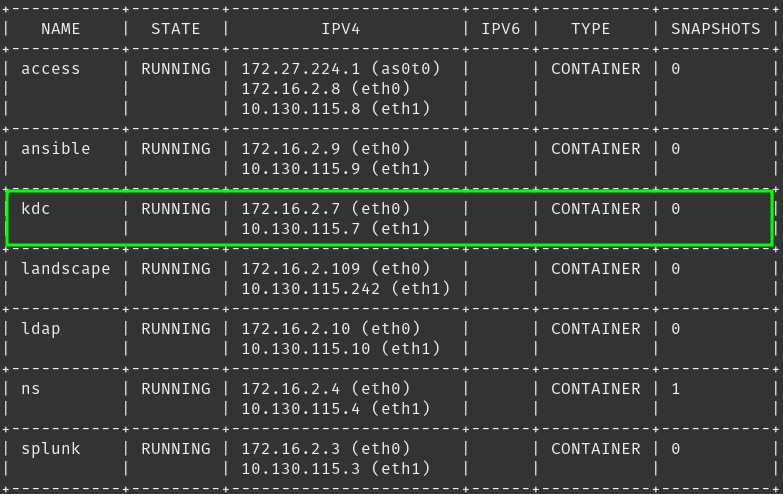
Ubuntu 22.04 | Install and configure a Kerberos Server
Adventures in the LXD Lab | Authentication Services As part of the lab and as a continuation of “Ubuntu 22.04 | In...
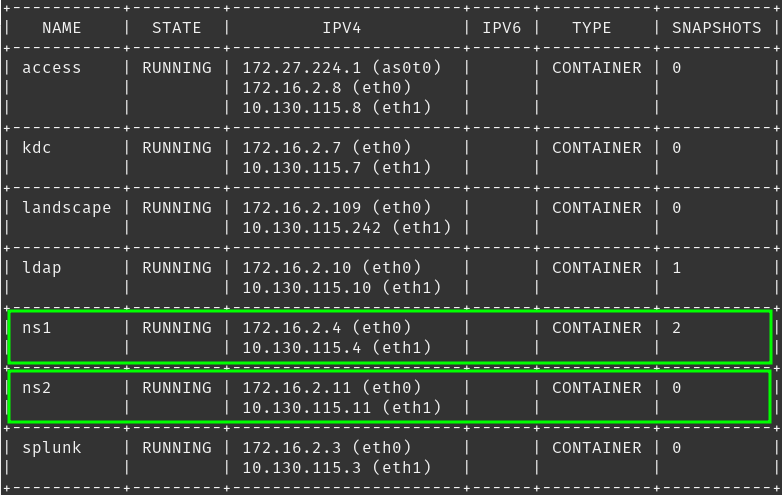
Ubuntu 22.04 | Install Bind DNS Server
Adventures in the LXD Lab | Name Resolution Services One of the core services that all devices browsing the internet or ...
Pop!_OS 22.04 | Window Lag Dragging/Moving
My Issue Recently, I decided to reinstall my OS (Pop!_OS) and post installation, I noticed the when dragging/moving wind...

Lenovo Chromebook Duet 5 Review: A tablet to rule them all?
Obligatory Intro I am typically not a fan of devices that do not provide a full-blown operating system with all of the b...
Kali Linux | Deploy it in a Docker Container
If you are like me, you prefer to not have to dual boot and certainly do not want to install Kali directly on your produ...
Personal Security Policy | Protect your digital life with 3 easy tips.
For most people it is common to be versed or at least aware of your organizations cyber security policy as part of ongoi...

Patching | Why it is important (Just Do It!)
Many users avoid patching for various reasons, such as having to reboot their computer -or- reluctance that patches may ...

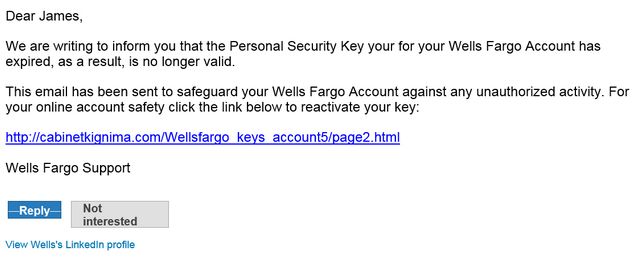
Multi-Factor Authentication | What is it and why you must have it!
In addition to following best practices for your passwords, Multi-Factor authentication is an additional safeguard used ...
Password Security | Best practices for secure and strong passwords
Password Security best practices are your first line of defense against account breaches. Unfortunately, many people und...
CentOS | Manage Auto Start services
Most server admins want their servers to run as lean and secure as possible. For that reason, we usually try to disable ...